
WordPress 7.0 Review: Biggest Changes Website Owners Need to Know
A comprehensive WordPress 7.0 review covering the biggest WordPress 7 features, performance gains, editor updates, and developer changes website owners should understand.






A new generation of SaaS startups is being built by tiny teams using AI, automation, and sharper product focus. Here’s why micro SaaS is thriving.

The browser market is changing fast as AI browsers challenge Chrome, Edge, and Arc. Compare speed, privacy, AI features, and which browser is best for modern work.

A practical visual comparison of Grok vs ChatGPT image editing for AI background replacement, with real-world examples, strengths, weaknesses, and workflow tips.

Explore the programming trends most likely to define future software development, from AI-assisted coding and platform engineering to Rust, WebAssembly, and secure-by-design systems.
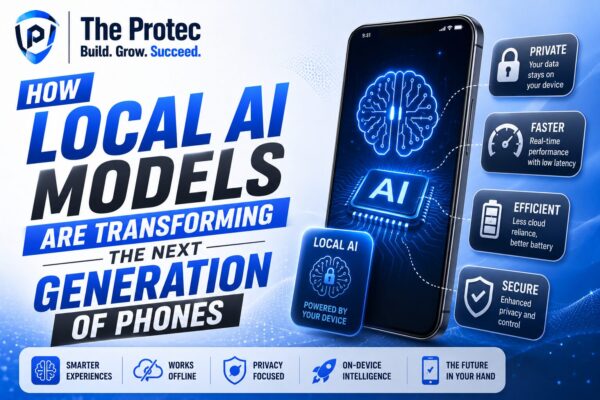
Local AI models are moving directly into mobile phones, enabling faster, more private, and more capable on-device experiences across AI phones and offline AI smartphones.

Developers are increasingly moving beyond React for faster builds, simpler architecture, and better performance. Explore the frontend frameworks gaining real momentum.
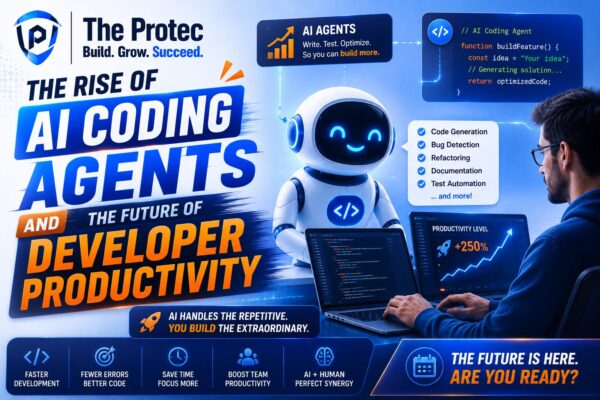
AI coding agents are moving beyond autocomplete into planning, coding, testing, and debugging. Here’s how they’re reshaping developer productivity and software delivery.

Developers are rethinking their stack as Bun delivers faster startup times, built-in tooling, and a smoother experience for modern web development. Here’s how Bun vs Node.js compares in real projects.

The most dangerous cybersecurity threats are often the ones businesses overlook. Learn which emerging risks are quietly growing into major enterprise security problems.
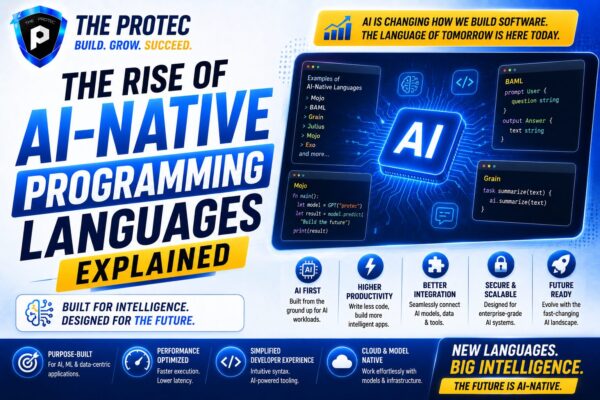
AI-native programming languages are reshaping how software is built, prompting developers to rethink syntax, tooling, and the role of code in AI software development.
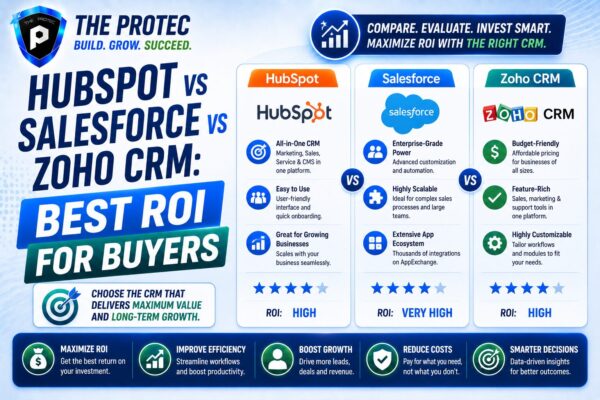
A data-driven comparison of HubSpot, Salesforce, and Zoho CRM to help buyers evaluate total cost, automation, scalability, and long-term ROI.

Foldable phones have evolved fast, but are they truly ready for everyday users? This deep dive examines durability, software, battery life, and real-world value.

Discover the underrated SaaS tools businesses are adopting to streamline work, boost productivity, and fill the gaps major platforms leave behind.