
Scratch Programming for Kids: A Beginner’s Guide
Learn Scratch programming for kids with this step-by-step beginner’s guide—complete with examples, stats, and actionable tips to get started today.

Learn Scratch programming for kids with this step-by-step beginner’s guide—complete with examples, stats, and actionable tips to get started today.

Discover proven crypto trading strategies to maximize investments. Learn risk management, technical analysis, and portfolio tips for success.
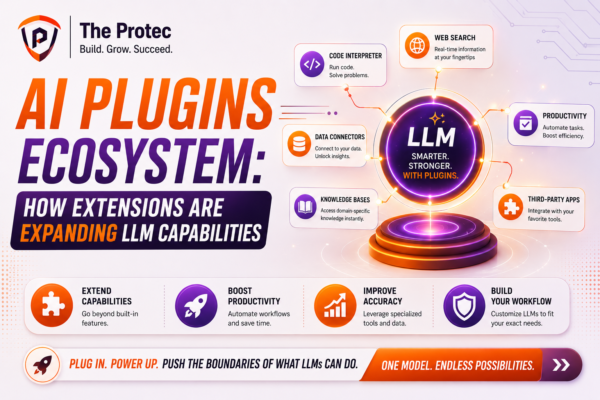
Discover how AI plugins and LLM extensions are transforming artificial intelligence by unlocking new use cases and expanding integration possibilities.
Which AI excels in deep research? Compare Gemini, ChatGPT & Perplexity’s multi-step analysis, accuracy, and speed to find your optimal AI research tool.
Discover why Jira is project management redefined. Explore features, real-world examples, and best practices to elevate your team’s efficiency.

Discover why smartphone performance today hinges more on AI-driven processing than raw GHz, highlighting the role of NPUs and evolving mobile benchmarks.

Developers are increasingly moving beyond React for faster builds, simpler architecture, and better performance. Explore the frontend frameworks gaining real momentum.

Discover how shadow AI unauthorized AI tools used by employees poses significant security risks and what enterprises can do to combat this growing threat.

best e-commerce platforms for online businesses in 2023. Featured platforms include Shopify, WooCommerce, Magento, BigCommerce, Salesforce Commerce Cloud and PrestaShop. These platforms offer rich features, extensibility and easy-to-use interfaces that help businesses build and manage successful online stores.
Learn how to sell digital products on Etsy with step-by-step strategies for optimizing listings, pricing, and scaling your shop. Start today!

Explore how AI wearables like smart glasses and earbuds are transforming personal tech by enabling always-on intelligence beyond smartphones.
Explore how personalized learning with AI reshapes education through adaptive tools, virtual tutors, and tailored curricula. Discover the future of EdTech.
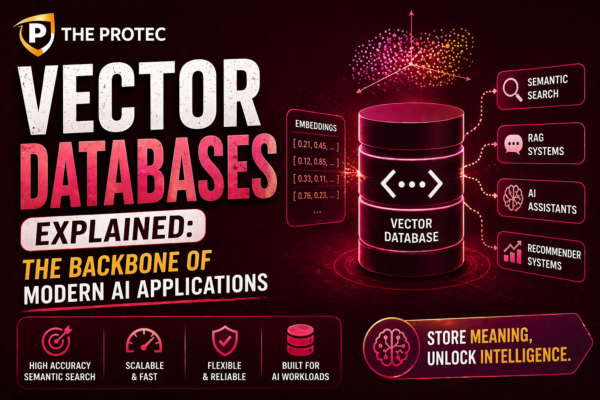
Explore how vector databases are transforming AI with embeddings search, powering semantic retrieval and retrieval-augmented generation systems.